

Securing Autonomous Defense Systems with Hardware-Attested Device Identity
Speakers: Hunter Hawke, Sr Solutions Architect and Josh Drake, Chief Technology Officer
Modern defense and “Neoprime” technology environments (like those pioneered by companies such as Anduril Industries) are redefining how systems operate. Autonomous platforms, edge compute, and AI-driven decision-making are becoming the norm.
But these systems introduce a fundamental challenge:
How do you trust what’s executing actions when there’s no human in the loop?
In these environments, traditional security models built around users, networks, and static infrastructure fall short. Access decisions must be tied to verified devices and trusted execution environments, not assumptions.
In this webinar, we’ll explore how device identity becomes a foundational control for securing next-generation, defense-grade systems.

Rethinking MFA for Non-Human Identities: Securing Workloads, Agents, APIs, and more
Speakers: Hunter Hawke, Sr Solutions Architect and Mike Malone, CEO and Founder
AI agents are quickly becoming a new interface to your most sensitive systems—calling APIs, accessing data, and taking actions on behalf of users. But there’s a problem:
MFA doesn’t translate to agents.
There’s no prompt to approve. No user to challenge. And once an agent has access, it often operates with persistent, reusable credentials that are easy to steal, replay, or misuse.
In many cases, that access is granted once and trusted far too long, with little visibility into how it’s actually being used.
In this webinar, we’ll explore what “MFA for AI” actually means—and why securing autonomous workflows requires a fundamentally different approach to identity and access.
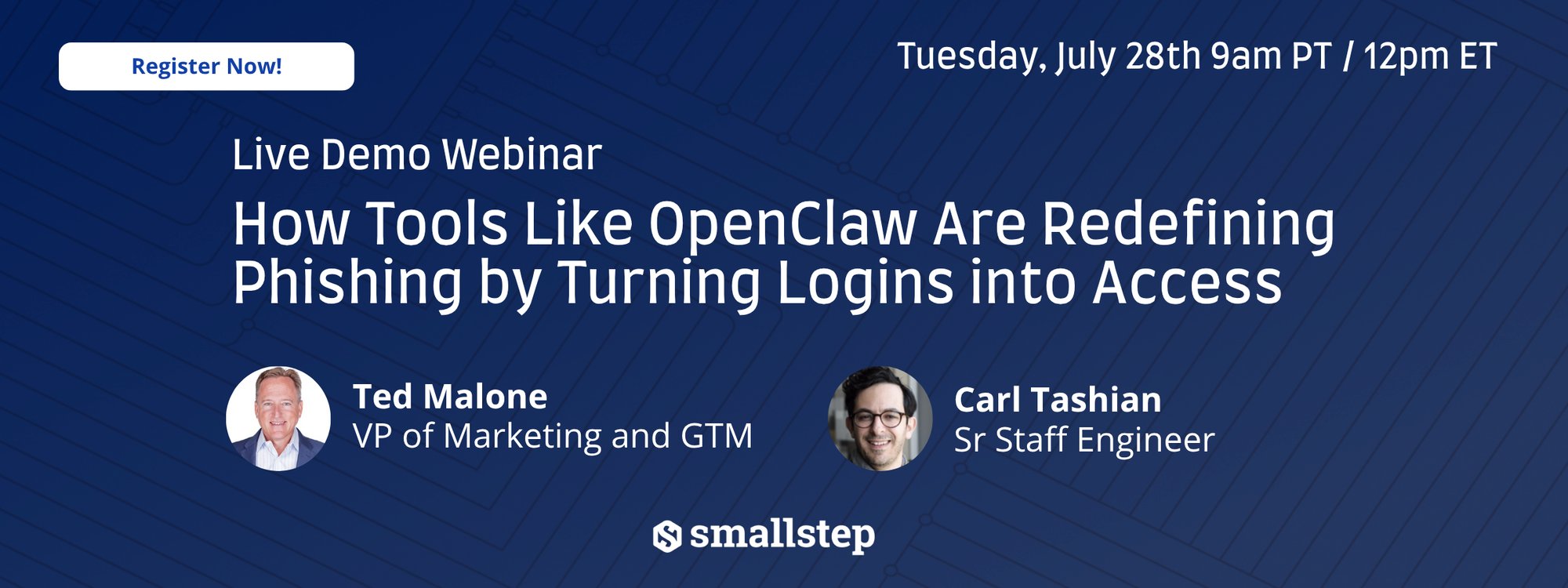
How Tools Like OpenClaw Are Redefining Phishing by Turning Logins into Access
Speakers: Carl Tashian, Sr. Staff Engineer and Ted Malone, VP of Marketing and GTM
Phishing attacks have evolved. It’s no longer just about stealing passwords—modern phishing kits can capture sessions, intercept tokens, and turn a single login into immediate access.
Tools like OpenClaw make these attacks easier than ever to deploy, giving attackers the ability to bypass traditional authentication flows and operate as legitimate users—often without raising alarms.
In this webinar, we’ll break down how modern phishing kits actually work—and why defenses built around credentials and logins are no longer enough.

Hacking Has Never Been Cheaper, and Phishing Has Never Been Easier
Speakers: Carl Tashian, Sr. Staff Engineer and Mike Malone, CEO and Founder
The cost of launching a phishing attack has never been lower—and the success rate remains dangerously high.
Today’s attackers don’t need sophisticated exploits. With off-the-shelf tooling, automated phishing kits, and readily available infrastructure, stealing credentials is cheap, fast, and scalable. And once credentials are compromised, most environments still allow access—especially when trust is based on users, not devices.
In this webinar, we’ll break down why credential phishing continues to be one of the most effective attack vectors—and what it actually takes to stop it.